Google account passwords have been stolenby hackers since the beginning of the Internet but as time passed they found,according to Bitdefender,newer and easier ways that are harder to catch with traditional heuristic detection.
Hackers took advantage on how Google Chrome displays their data(URIs-Uniform Resource Identifiers) in their phishing attack, although Mozilla Firefox users suffered from this aswell.
CatalinCosoi, Chief Security Strategist at Bitdefenderexplains what hackers aim for with this scheme:“With access to users’ Google accounts, hackers can buy apps on Google Play, hijack Google+ accounts and access confidential Google Drive documents.The scam starts with an email allegedly sent by Google, with “Mail Notice” or “New Lockout Notice” as a subject.”
Below you can see a photo of an e-mail that frauds use to trick users: “This is a reminder that your email account will be locked out in 24 hours. Due to not being able to increase your Email storage Quota.Go to the INSTANT INCREASE to increase your Email storage automatically.”
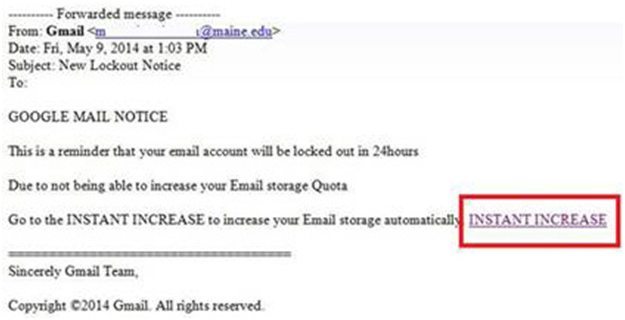
What happens when clicking the INSTANT INCREASE link?Users are redirected to a Google login web page that imitates the authentic one and asks for their credentials.
“What is interesting about this phishing attack is that users end up having the “data:” in their browser’s address bar, which indicates the use of a data URI scheme,” continues CatalinCosoi.
Schemersmanage to include in-line data in web pages as if they were external resources by using Base64 encoding. Base64 encoding role is to represent file contents, supplying the content of the fake web page in an encoded string within the data URI.
It is hard for regular users to understand what is happening,as Google Chrome doesn’t show the whole string so the cyber-criminals exploit their lack of knowledge.
These being said, it is common for scammers to pose as services that contact people by e-mail for announcements or notifications. Among phishers’ favoritedisguises we haveGoogle, Facebook, eBay, PayPal, phone services and financial institutions. The most recent attack wanted to access users’ Gmail credentials, by targeting Google Drive’s landing page.

